In today's rapidly evolving digital landscape and with the constant growth in the number of cyber threats of all kinds, ensuring the security of business data is one of the highest priorities for organizations of all types and sizes. Microsoft 365 Defender (now Microsoft Defender XDR) in this context presents itself as a complete and integrated solution for protecting digital work environments and sensitive data and is one of the most solid cybersecurity solutions offered by the Redmond company. In this article, we'll explore its key features, benefits, and available licenses, offering an overview of its advanced protection capabilities and intuitive management of security activities.

Cybersecurity is becoming an increasingly important issue in the contemporary digital landscape, with companies and organizations around the world investing significant amounts of money to better protect their IT infrastructures. In this scenario, Microsoft has not stood idly by and has been committed, on the contrary, since the dawn of cybersecurity, to the fight against cyber threats to protect its users and customers.
Microsoft 365 Defender (now Microsoft Defender XDR) is a complete solution for business data security and of the digital work environment in which these are created, collected and exchanged. It is based on an advanced protection system, which combines the action of four main products of the suite for threat prevention, monitoring and response. Its strength lies in its holistic nature, which allows an integrated and coordinated management of security activities.
Defender can become a critical component of any organization's cybersecurity strategy, and by taking advantage of its advanced threat detection and response capabilities, complete visibility, affordability, and simplified management, companies can improve their security posture and stay one step ahead of the dangers of the digital world.
But how does it work and what are the advantages offered by its implementation to users and businesses? What are its strengths and limitations? Let's find out one step at a time in the next sections.
Microsoft 365 Defender, as we mentioned in the introduction, is an integrated suite of advanced security and threat management tools developed by Microsoft to protect corporate digital infrastructure. It offers a holistic approach to cybersecurity, detecting and responding to threats in real time, combining advanced protection capabilities through different Microsoft 365 cloud services. Microsoft 365 Defender (now Microsoft Defender XDR) can detect complex attacks, correlate events from multiple sources, and orchestrate automated responses to mitigate persistent and sophisticated threats, reducing response times and improving the overall security of the business ecosystem.
The tools that make up the suite work in synergy within the suite, providing a centralized threat monitoring and management system that simplifies incident response and increases the resilience of the corporate digital infrastructure against advanced threats.
This system acts natively, coordinating the activities of detection, prevention, investigation and response to incidents between endpoints, identity, e-mail and applications, which is possible thanks to the combination of the services of the four main products that make up the suite, which are respectively:
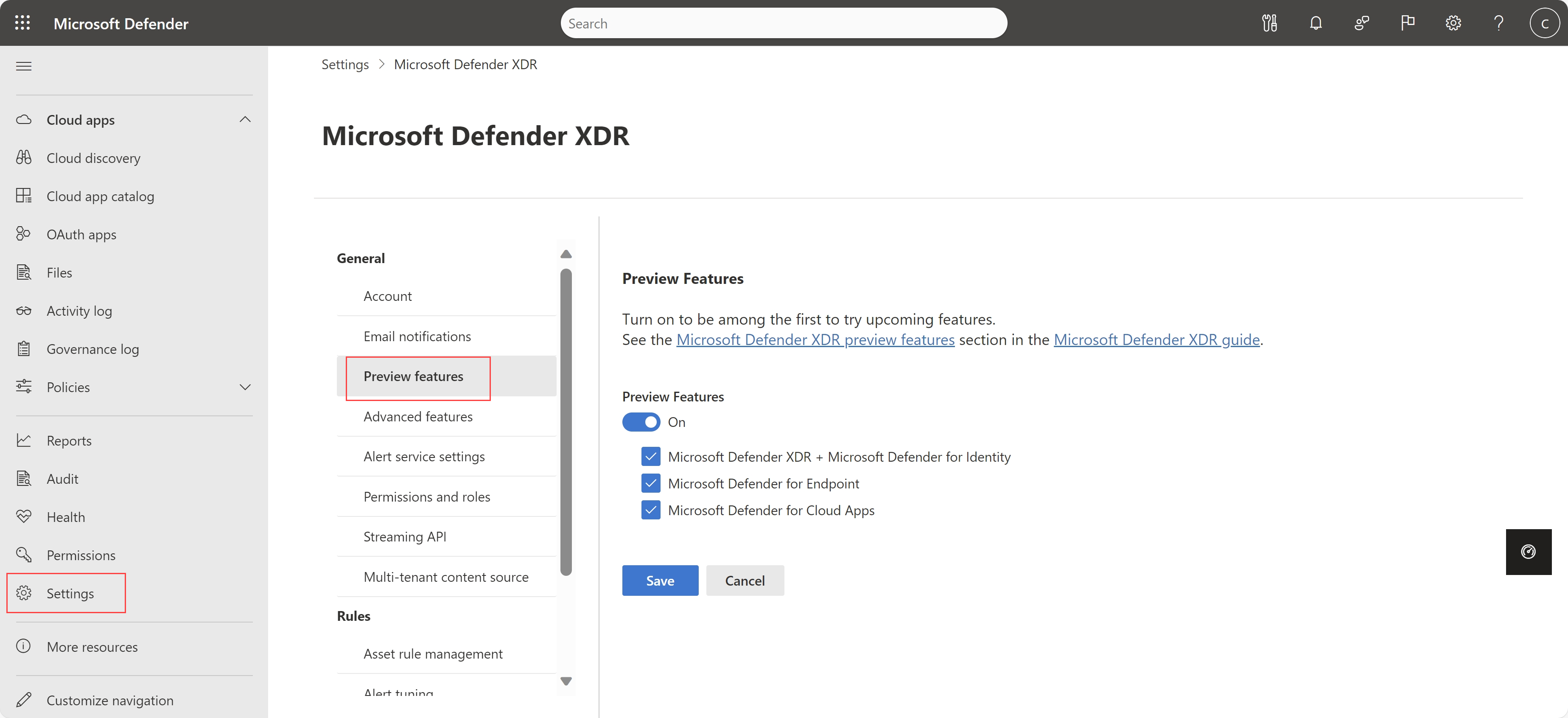
The operations performed by these products are centralized in the Microsoft 365 Defender portal, which provides a unified dashboard to monitor events on various endpoints, devices, and apps. The system offers an intuitive interface that allows administrators to manage security activities in real time and in a synchronized manner. In addition, it provides reports and statistics to analyze past events, identify present threats and to predict future ones.
In addition, the system has recently been enriched by artificial intelligence and machine learning features, which make it possible to improve over time the ability to recognize and combat the most common and sophisticated computer threats, such as malware, phishing, ransomware and zero-day exploits.
Automating incident response with Microsoft Defender XDR delivers a range of benefits that impact both the organization as a whole and the IT team. Here are the main ones:

Before exploring the specific benefits that Microsoft 365 Defender brings to a business, it's important to understand the types of licenses available to access them.
In addition to having specific licenses for each of its products, Microsoft 365 Defender (now Microsoft Defender XDR) is included in the following:
It is sufficient that the user has one of the licenses listed here to access the services and functionalities of the system from the relevant portal.
To successfully implement business processes within the Microsoft 365 ecosystem, the following skills are needed:
Dev4Side Software has the vertical technical skills to provide you with a single, transversal point of contact for all the elements of your subscription.
So just buying the right license is enough? Not exactly. An important fact to underline concerns product activation and to activate Microsoft 365 Defender, you must have one of the following roles: Global Administrator or Security Administrator.
To activate Microsoft 365 Defender (now Microsoft Defender XDR), you must have one of the following roles: Global Administrator or Security Administrator. Other roles allow access to functionality but not system activation. Among these are:
Therefore, in addition to considering the type of license subscribed to, it is essential to pay attention to the role assigned by your company to avoid misunderstandings and ensure effective use of Microsoft 365 Defender services.
Microsoft 365 Defender (now Microsoft Defender XDR) has a whole range of benefits for those companies that want to optimize costs to protect IT infrastructure, to optimize the efficiency of threat detection and response, to reduce exposure to risks and to optimize the management of security activities.
But what are these advantages in concrete terms? Let's see the main benefits of implementing Microsoft 365 Defender to protect your organization's digital infrastructure in the convenient list below:

Microsoft 365 Defender has a number of notable strengths, as highlighted above. However, it is also important to recognize its weaknesses, to which users, especially administrators and the IT team, must pay attention to if they want to be able to get the most out of the functionality of the suite and not find themselves in unpleasant situations while carrying out their operations.
The good news is that with a few precautions it is possible to avoid damage and to maximize the effectiveness of Microsoft 365 Defender (now Microsoft Defender XDR) and its tools. So here are some suggestions on how your IT team can address these challenges:
Addressing these challenges proactively can help to ensure effective and reliable protection of the digital workplace through Microsoft 365 Defender (now Microsoft Defender XDR).
Cybersecurity has never been more crucial in the world of data protection than it is today, with organizations around the world working hard to ensure the security of their critical business data.
The investments made in recent years in cybersecurity by large development houses such as Microsoft are just another sign of a digital landscape that, as its complexity grows, is becoming increasingly dangerous for users and companies to navigate without the right protection measures.
With its functionalities and limitations, Microsoft 365 Defender (now Microsoft Defender XDR) presents itself to users and organizations that wish to protect themselves from the risks of the digital world as an incredibly robust solution to combat current cyber threats and keep their employees and their daily activities safe.
Therefore, all that remains is to invite you to deepen the topic on our pages (where we also talk in more detail about the rest of the Microsoft products dedicated to the field of IT security) and to experience first-hand the features of Microsoft 365 Defender to find out if it may also be the right solution for your cybersecurity needs.
1. What is Microsoft 365 Defender?
Microsoft 365 Defender (now Microsoft Defender XDR) is an integrated Extended Detection and Response solution that unifies detection, correlation, and response to security incidents across endpoints, identity, email and collaboration tools, and cloud apps, through a centralized portal.
2. What does' XDR 'mean and how is it different from antivirus?
XDR (Extended Detection and Response) goes beyond traditional endpoint or antivirus protection: it correlates signals from multiple domains such as devices, identities, email, and applications to detect complex attacks and orchestrate automated responses, reducing analysis and containment times.
3. Which products make up Microsoft 365 Defender?
In this context, the suite combines four main components: Defender for Endpoint, Defender for Office 365, Defender for Cloud Apps, and Defender for Identity.
4. What threats can Microsoft 365 Defender detect?
It supports the detection and response to threats such as malware, phishing, ransomware, and advanced attacks, including zero-day exploits, through event correlation and the use of artificial intelligence and machine learning.
5. What are the main benefits for a company?
The most common benefits include integrated coverage across the Microsoft ecosystem, centralized management, faster response times, automation of operational activities, improved visibility, and greater overall resilience against advanced threats.
The Infra & Security team focuses on the management and evolution of our customers' Microsoft Azure tenants. Besides configuring and managing these tenants, the team is responsible for creating application deployments through DevOps pipelines. It also monitors and manages all security aspects of the tenants and supports Security Operations Centers (SOC).